in Sunday’s New York Times, round-up reporting on the emergence of the Stuxnet worm, last year’s breakout malicious code, which spread to offline industrial control systems by way of thumb drives, and seemingly was targeted at Iran’s nuclear program. The Times story recounts the work of Richard Langner, the psychologist-turned-computer-security specialist who worked out that the worm targeted a specific configuration of industrial controllers:
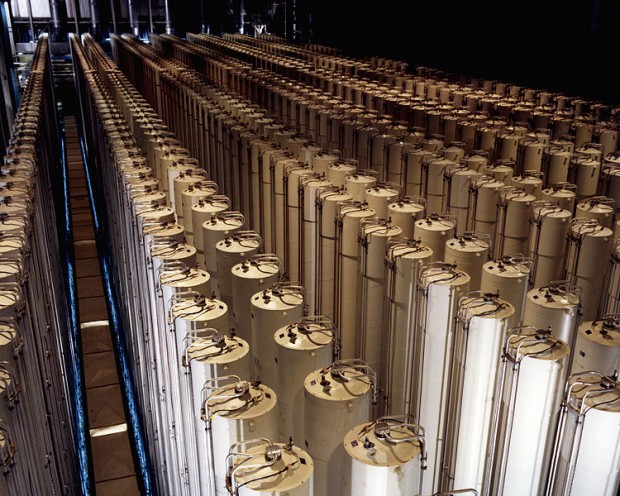
But as Mr. Langner kept peeling back the layers, he found more � what he calls the �dual warhead.� One part of the program is designed to lie dormant for long periods, then speed up the machines so that the spinning rotors in the centrifuges wobble and then destroy themselves. Another part, called a �man in the middle� in the computer world, sends out those false sensor signals to make the system believe everything is running smoothly. That prevents a safety system from kicking in, which would shut down the plant before it could self-destruct.
Langner concluded that in contrast to many examples of malicious code, Stuxnet was not designed for showing off technical prowess, but for “destroying its targets with utmost determination in military style.” His forensic work provides strong circumstantial evidence that the worm was engineered by American and Israeli specialists.
It’s also clear that Stuxnet was designed to mark its targets with extraordinary precision. But future makers of malicious programs targeting offline machinery won’t be so clinical. As everyday objects increasingly are knitted together into interpenetrating networks, will viruses spread to everyday machinery? How long before my coffeemaker or (far more ominously) the navigation computers of airliners come down with viruses? And for those who imagine the Singularity as either Armageddon or Apotheosis, a more complicated picture is possible: even as transcendent machines, we’re likely to come down with nasty colds.
 Gearfuse Technology, Science, Culture & More
Gearfuse Technology, Science, Culture & More



You guys are even more dimwitted that you sound.!
Can’t you see that this program is just the tip off the iceberg?
These capabilities will , if they are not already beieng used, to attack any machine for any reason that the controlling governments may desire!
Do you actually think that their are any secure digital signatures that can not be easily broken by this technology? Do you actually think that when you get virus definition updates or windows updates for that matter, that they are not easily corrupted for the attackers purpose whatever that may be?
Remember power corrupts and absolute power corrupts absolutely!
Also the writers make billions of dollars on these products so they are carefull who they attack.
To keep the modicum of respectability and plausible deniability that it is in use now!
Also unlike LINUX where the source code is freely available, not the compiled run time code
That us poor souls are sold a bill of goods too that can not be uncompiled to expose it’s vulnerabilities
we are left to the whims of the powerful who own the source code.
That is the key that leads to all of our vulnerability! Hackers could stop these attacks with access to source code BUT THEY AREN’T ALLOWED THAT CRITICAL ACCESS!
GIVE ME A BREAK AND START GETTING SMART YOU DUMMIES!